An Android virus that disguises itself as Google+ and overhears your conversations has been recently discovered by Trend Micro, a major security software developer.
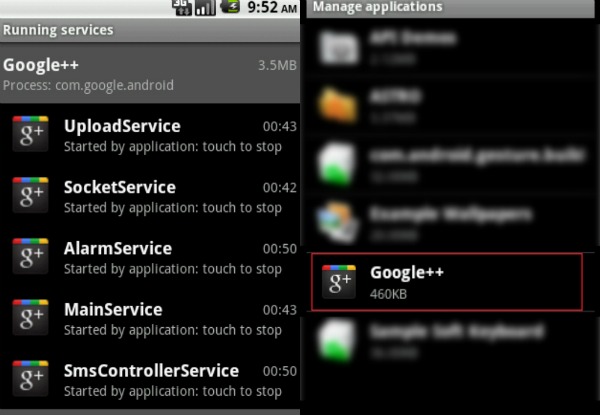
The malware is called ANDROIDOS_NICKISPY.C and brings into play the following services on your mobile phone:
- AlarmService
- CallLogService
- CallRecordService
- CallsListenerService
- CommandExecutorService
- ContactService
- EnvRecordService
- GpsService
- KeyguardLockService
- LocationService
- MainService
- ManualLocalService
- RegisterService
- ScreenService
- SmsControllerService
- SmsService
- SocketService
- SyncContactService
- UploadService
As the services are displayed with the Google+ icon in the task manager, there is apparently no reason to be suspicious of anything. However, the malware itself appears as Google++, so it is very important to check the name with great attention. Basically, an extra + makes the difference between private communication and conversations that are heard and maybe recorded by malevolent people.
The port 2018 is used for uploading the recorded conversations to a certain URL. One thing to keep in mind is that the malware does more than just uploading any audio that it records. Along with this, your call logs, text messages and even GPS coordinates can be accessed.
The developer of the virus obviously put a lot of work into it. Additional features of the malware include the ability to answer incoming calls automatically, as well as control via text messages. Still, in order to be able to do these, there are certain criteria that must be met. The incoming call must come from a certain number that is specified in the configuration file of the malware. In addition, the phone needs to be in stand-by for this to work. When the call is received, the phone is turned to silent mode, to make sure that you do not notice anything. Next, the dial pad gets hidden and the home screen is displayed. After this stage, everything that is in the range of the microphone is recorded and uploaded, along with other types of data.
This malware is a lot more dangerous than ANDROIDOS_NICKISPY.A and ANDROIDOS_NICKISPY.B, which were only able to record phone calls. In order to avoid the infection with this type of malware you are recommended to use caution while downloading Android apps from the Web. In addition, make sure you use reliable sources for these apps. ANDROIDOS_NICKISPY.C only affects smartphones based on Android 2.2 or earlier. Android 2.3 users are safe, as the MODIFY_PHONE_STATE parameter is disabled, in their case.